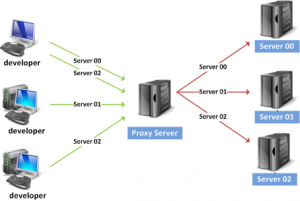
An internet proxy server goes about as an arbiter between a web server and the customer PC. They line all web activity existing between the Internet and the Intranet. These web servers can execute every single key capacity as much following Internet convention addresses, different URL, time and date of operation, and number of bytes downloaded. Every one of these points of interest can be truly substantive when dissecting any sort of assault against a system. With the assistance of intermediary servers, Intranet directors can set up better get to and give better administrations to their workers.
At whatever point a PC on the Intranet asks for the Internet to recoup certain subtle elements or a page from the web server, the interior PC reaches the intermediary PC. At that point it associates with the Internet server, which gives the craved site page to the proxy server. The intermediary then passes this subtle elements or site page back to the machine on the Intranet. Another zone where there’s wide utilization of intermediary destinations would be to store sites and records to quicken access. This truly is most applicable with sites which have sporadic movement level.
A few internet proxy servers require the utilization of certain unique proxy customers. Numerous gathering take after the prominent methodology of utilizing arranged customers with servers. In any case, while utilizing such a customer, guarantee that the intermediary customer is uncommonly arranged to work from a setup menu and with servers.
Proxy servers can likewise be utilized to actualize security plans. In case, document transference convention server can permit the obliged records to be sent to the PC on the Intranet from the Internet. It can likewise keep the transmitting of records from the net to the sorted out system, and the other way around. Along these lines, the Intranet executives can impediment any disposable individual particularly from outside the association from acquiring vital corporate information.
Numerous organizations likewise utilize proxy servers to accelerate the execution of certain Internet benefits by concealing information keeping duplicates of the needed information. In case, a web proxy server can conceal various site pages.
Accordingly, if any individual from the Intranet needs to obtain entrance one of the shrouded site pages, he/she can without much of a stretch get it from the intermediary server crosswise over fast lines of the Intranet, as opposed to going out crossways the Internet and access the site page at a lower velocity from the Net lines. These are a few structures in which the intermediary servers work to advantage the managers.